TIME-BASED PROOF INFRASTRUCTURE
Proof infrastructure for AI accountability and event chronology.
TimeChain2 creates a live, machine-verifiable record of prompts, actions, approvals, state changes, and outcomes for systems where responsibility depends on sequence and context.
Built for the moment when an AI system must explain who triggered what, under which instructions, in which context, and in what order.
WHY NOW
The first major AI liability crises will be fought on chronology: who acted, under whose authority, with which prompt or approval, and in what operational context.
When AI systems cause damage, accountability will depend on reconstructing the exact chain of prompts, decisions, validations, interventions, and outcomes. TimeChain2 was designed to make that chain visible and verifiable.
AI ACCOUNTABILITY
The next major AI failure will immediately become a responsibility investigation.
When an autonomous or semi-autonomous system causes real damage, the first serious questions will not be theoretical. Investigators, regulators, insurers, courts, operators, and counterparties will need to reconstruct who triggered what, under which instructions, in which operational context, and in what sequence.
TimeChain2 was designed for that layer of reality. It does not assign legal blame by itself. It creates a verifiable chronological trace around prompts, machine actions, approvals, interventions, state changes, and outcomes, so accountability is not rebuilt later from incomplete logs or disputed timelines.
Prompt chain, model action, human approval, system state, downstream effect.
Fragmented logs, missing context, disputed timelines, and no common proof layer.
A time-ordered, machine-readable trace that preserves sequence as evidence.

WHY NOT BITCOIN
A different trust model for a different problem.
Bitcoin is built for permissionless global consensus in adversarial environments. That design comes with deliberate latency and high energy cost. TimeChain2 is built for a different class of systems: fast, machine-readable event chronology with a much lighter computational footprint.
The comparison is not that TimeChain2 replaces Bitcoin. It does not. The comparison is that it provides a faster and lighter proof layer because it is solving a different problem: verifiable sequence, operational traceability, and visible proof publication rather than open monetary settlement.
USE CASES
 Audit trails
Audit trails
Build a chronological record for actions that must remain defensible over time: approvals, policy changes, technical interventions, operational incidents, or internal control steps. The value is not just storage. The value is proving sequence.
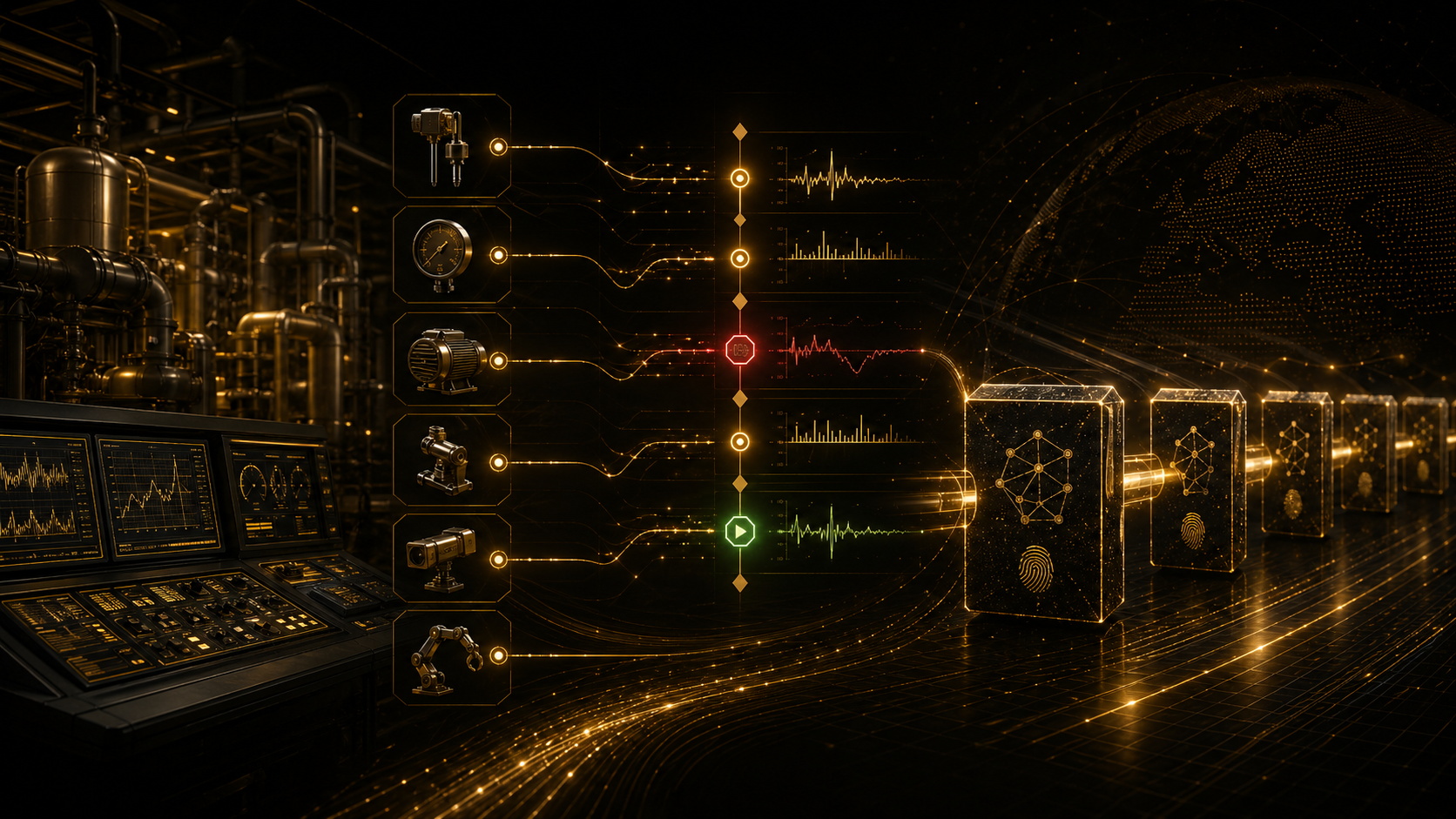 Industrial logs
Industrial logs
Track machine events, process changes, equipment state transitions, and execution traces in environments where a timestamp alone is not enough. In industrial systems, proving which event happened before another can matter as much as the event itself. A shutdown command, a sensor anomaly, a maintenance override, and a restart event do not have the same meaning if their order is disputed after an incident.
 Compliance records
Compliance records
Expose verifiable execution traces for regulated or audited environments. This is relevant when an organization needs to demonstrate not only that a record exists, but that a sequence of actions occurred in the documented order. Think approval chains, policy acknowledgements, document releases, control checks, or escalation steps where chronology is part of the compliance evidence itself.
PROPERTIES
HOW IT WORKS

TimeChain2 starts from raw events, imposes deterministic chronology through its proof process, and publishes signed outputs that external parties can inspect. The point is not only to record activity. The point is to make sequence itself verifiable.
INTERFACE
The interface below exposes the current state of the running chain in real time: system status, incoming events, active block state, and the latest signed proof block.
WHAT IT DOES
Turns chronology into evidence.
TimeChain2 transforms event chronology into a proof layer. Instead of keeping timing and sequencing buried inside private infrastructure, it exposes a visible and verifiable record that external parties can inspect.
WHERE IT HELPS
Critical when trust depends on sequence.
It is relevant wherever value depends on chronology: proving what happened first, when a record changed, whether a workflow was altered, or whether a machine trail remained intact after execution.
PRACTICAL USES
A proof layer for high-value systems.
Anchor critical records, publish machine events, detect silent tampering, expose execution traces, and strengthen trust across distributed systems, industrial processes, and regulated environments.
GAMING / LOOT PROVENANCE

A market where chronology itself has value.
In games and digital economies, valuable items do not only need ownership records. They can also benefit from provable issuance history: when a loot item was dropped, under which conditions, in which sequence, and whether its state or provenance changed over time. That creates a new layer of trust for rare digital objects, event-based rewards, and machine-generated asset flows.
MEDIA / FILE CERTIFICATION
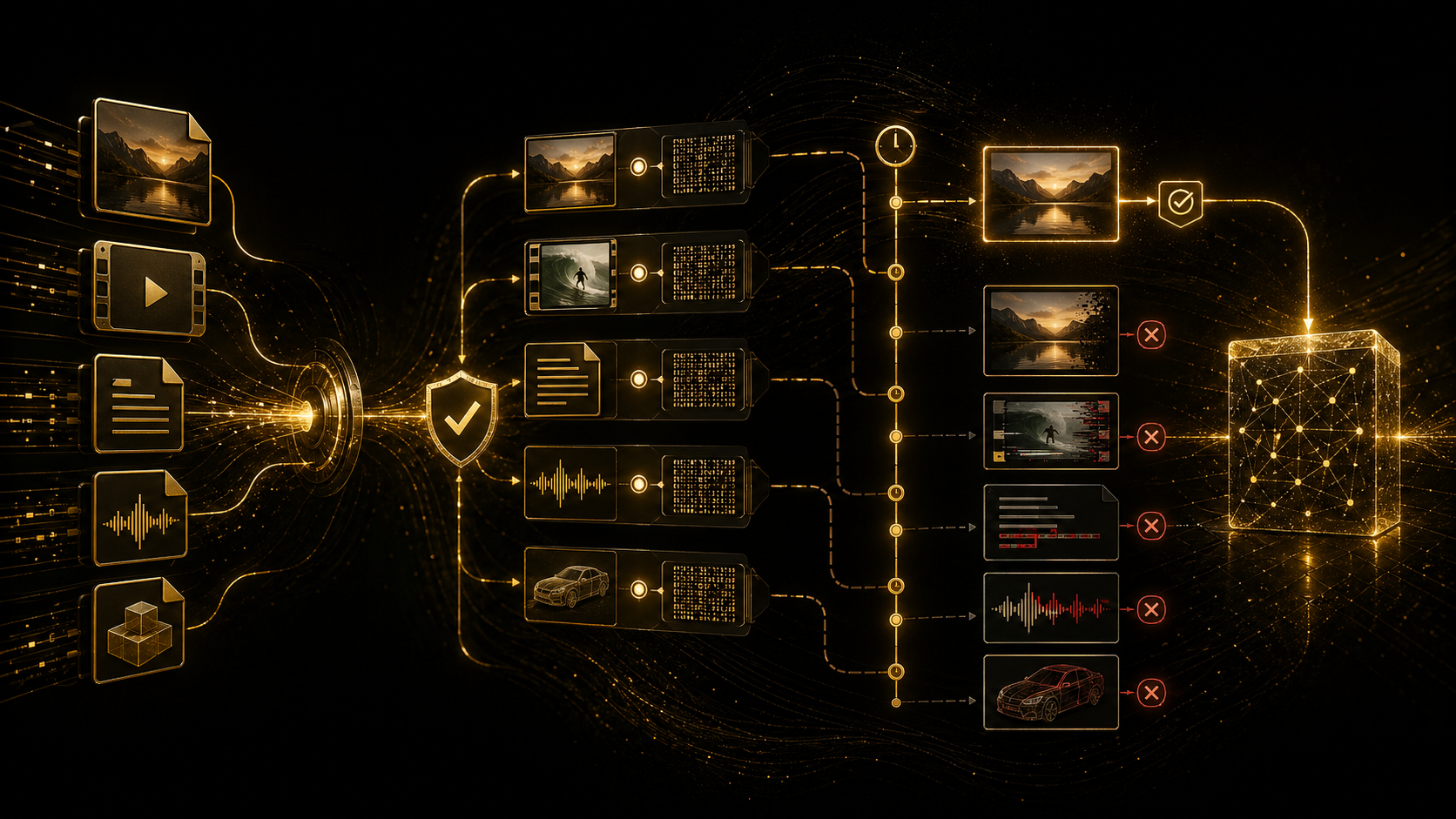
An anti-fake and integrity layer for digital content.
TimeChain2 can be used to anchor content hashes, preserve publication order, and expose integrity evidence for files, images, video, or generated media. The purpose is not magical truth detection. The purpose is to create a visible proof layer around origin, chronology, and tamper evidence, which is especially relevant in an environment where synthetic media and manipulated files are becoming easier to distribute.
EXAMPLE SCENARIOS
A plant operator needs to reconstruct why a line stopped. Sensor threshold breach, controller command, operator intervention, and restart sequence are all visible in the published order, which makes post-incident analysis harder to rewrite after the fact.
A regulated workflow requires evidence that review, approval, release, and notification happened in the expected order. TimeChain2 does not replace the business system; it adds a proof layer around the chronology that external auditors or counterparties can inspect.
A newsroom, studio, or creator can publish a content hash when a file is produced, then prove whether later versions are derived edits, re-encodes, or unrelated files. That is useful when origin, release time, and tamper evidence matter more than storage.
LIVE MONITOR
The split-flap panels below are connected to the active backend and update from the live chain, showing how the proof infrastructure behaves in production time.
TIMECHAIN2
Public time-proof feed